
Why Incognito Mode Won't Replace Antidetect Browsers When Working with Traffic
Incognito mode is still perceived as an anonymity tool. The logic seems simple: the browser doesn't save history, deletes cookies after the session, and doesn't remember form data, so you don't need to worry about account confidentiality.
The problem is that incognito mode doesn't change your digital fingerprint or isolate accounts, so for websites, you're still the same user.
In this article, we'll break down in detail how exactly websites identify users, why basic anonymity tools aren't enough, and how antidetect browsers solve this problem at the technical level.
How Incognito Mode Actually Works
Incognito mode is a local "sandbox" inside the browser. It's not designed to protect against tracking and doesn't hide you from websites. It performs several basic tasks:
- Doesn't save browsing history
- Deletes cookies and cache after closing the tab
- Doesn't remember entered data, including logins and forms
This mode is convenient if you're using someone else's computer or secretly searching for a gift. In this case, logins and search history won't be saved and won't be seen by others.
All of this works only inside the browser. Incognito mode doesn't hide your IP address, doesn't encrypt traffic, and doesn't change device parameters. For websites and anti-fraud systems, this is the same user with the same device and the same set of parameters.
How Websites Track Users
Websites stopped relying exclusively on IP addresses and cookie files long ago. These methods are easily bypassed by basic tools, so security systems have moved to a new level. Today, the main and most reliable identification method is the browser's digital fingerprint.
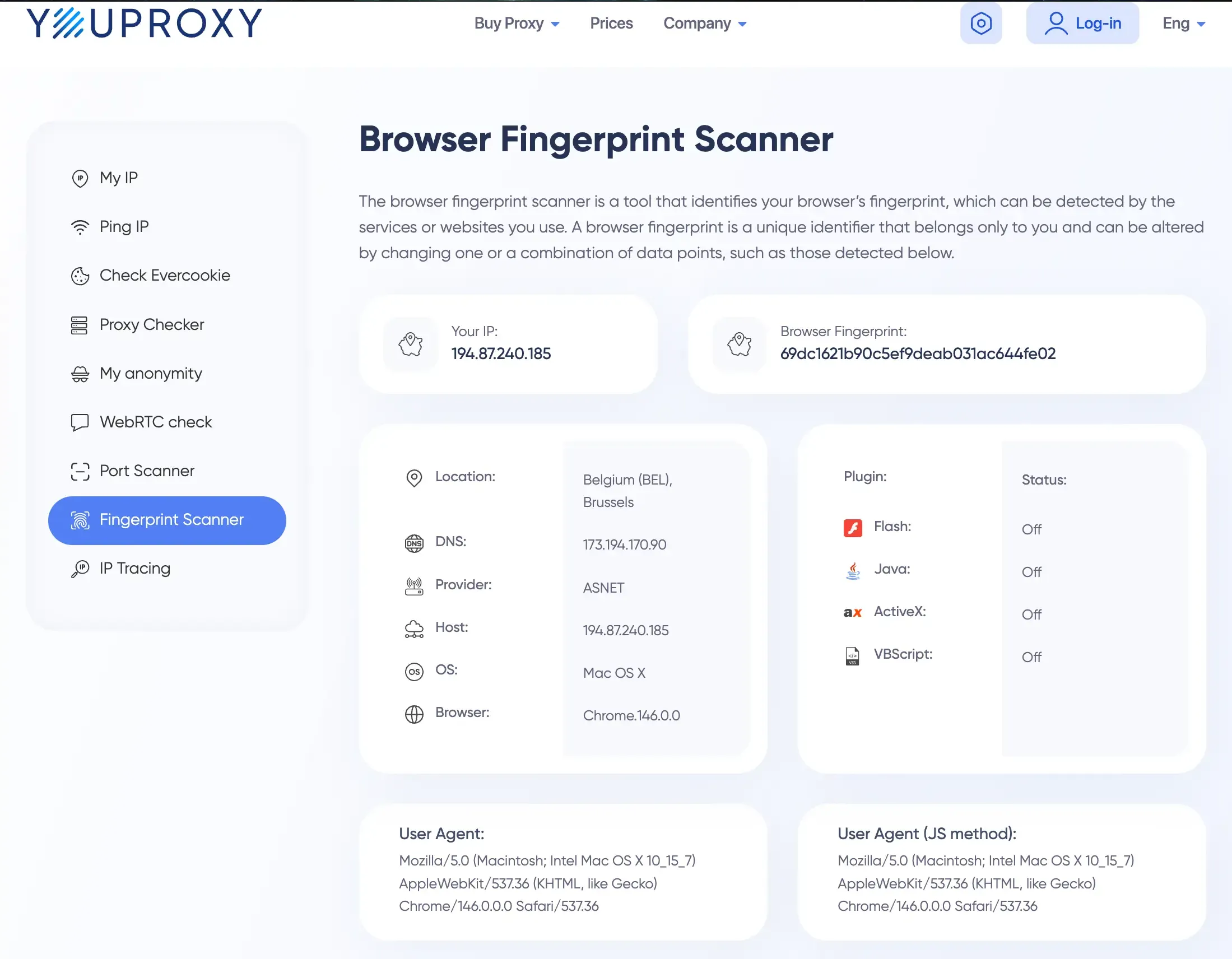
This is a unique set of technical parameters of your device that is formed automatically and unnoticed by you at the very moment you visit a website. Site scripts poll your system in milliseconds and collect data. This array includes:
- Graphics characteristics (WebGL, Canvas). The site sends a hidden command to your video card to render an invisible 2D or 3D shape. Due to microscopic differences in chip architecture, driver versions, and operating systems, the final render always differs mathematically. The system remembers this unique graphics hash.
- Audio processing (AudioContext). A similar principle is applied to sound. A low-frequency audio signal is generated and run through your sound card's algorithms. How your "hardware" distorts the sound wave forms a unique audio fingerprint that cannot be hidden through standard settings.
- Number of processor cores and memory amount. Through basic JavaScript commands, the site instantly learns your computing power. This narrows the search: if you have a 16-core processor and 32 GB of RAM, you already stand out from the mass of users with office laptops.
- User-Agent (OS and browser). A basic text string that tells the target server the version of your browser and operating system.
- Screen resolution. Not only the standard monitor resolution is analyzed (e.g., 1920x1080), but also the available working area (accounting for the taskbar), color depth, and individual system scaling parameters.
- List of installed fonts. One of the most accurate markers. The script checks for the presence of hundreds of different fonts in your system. Your personal set of standard and downloaded designer fonts is unique and identifies you more accurately than a passport.
- System language and timezone. Sites read your system time settings and language priorities in the browser. If they conflict with the geodata of your IP address, anti-fraud immediately marks you as a suspicious user.
Additionally, WebRTC technology is actively used. It is designed for direct audio and video calls through the browser, but its main vulnerability is that it can reveal your real local and public IP address even when working through a reliable proxy server or VPN application.
All these parameters are collected together, like pieces of one puzzle, and form a unique device profile. And the main problem is that neither a banal IP change nor launching a new tab in incognito mode affects this data array in any way. The protection system will still see the same user behind the same computer.
How Antidetect Differs from Incognito
If incognito mode is an attempt to delete local traces after a session, then antidetect is a reworking of the browser itself at the architecture level. Typically, such solutions are built on custom Chromium or Firefox builds and substitute kernel-level data.
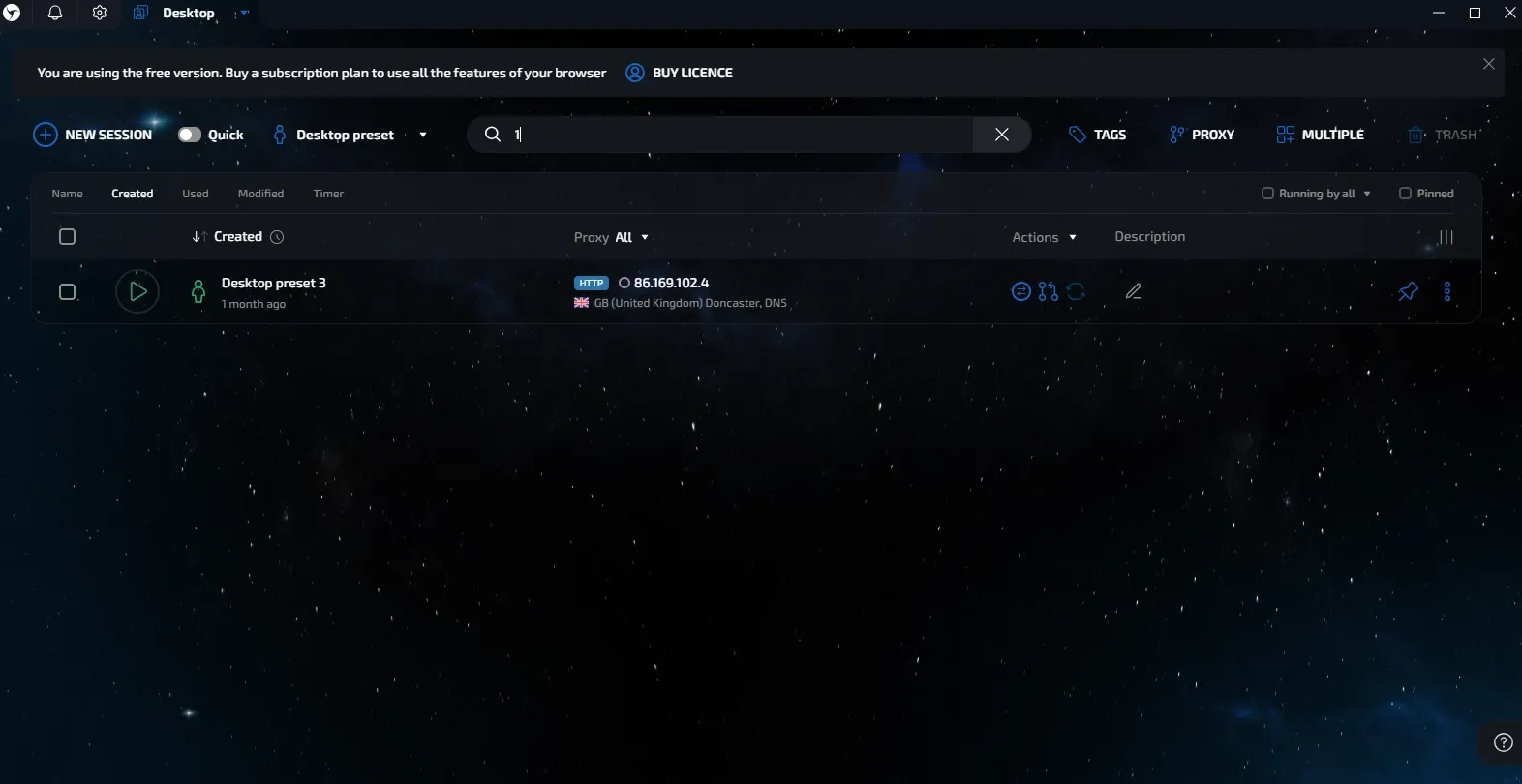
Antidetect hides data while transmitting a correct and logical set of characteristics to the system. These parameters look the same as an ordinary user's, but form a separate profile.
Let's look at how this is implemented at the technical level.
Hardware Fingerprint Substitution
Antidetect isn't limited to changing the User-Agent. It intervenes in the browser's interaction with the device. When processing graphics (WebGL, Canvas), controlled distortion is added, which changes the final hash.
At the same time, the system continues to see the real video card, but with unique characteristics. AudioContext, MediaDevices (cameras and microphones), and system fonts are processed similarly. In advanced solutions, such as Linken Sphere, databases of real fingerprints are used so the profile looks like an ordinary device.
Isolated Data Containers
Incognito mode deletes cookies, but modern trackers use other storages: LocalStorage, IndexedDB, Service Workers, and similar mechanisms. In antidetect, each profile is a separate environment with its own data storage system. Profiles don't intersect with each other. Upon re-entry, all session data is preserved.
Traffic Routing Through Kernel-Level Proxies
Using proxies through extensions in a regular browser often leads to leaks. For example, WebRTC can transmit the real IP directly. In an antidetect browser, the proxy is integrated deeper, at the network stack level. All traffic passes through the specified node. If the connection breaks, protection kicks in that blocks data transmission and prevents real IP leakage.
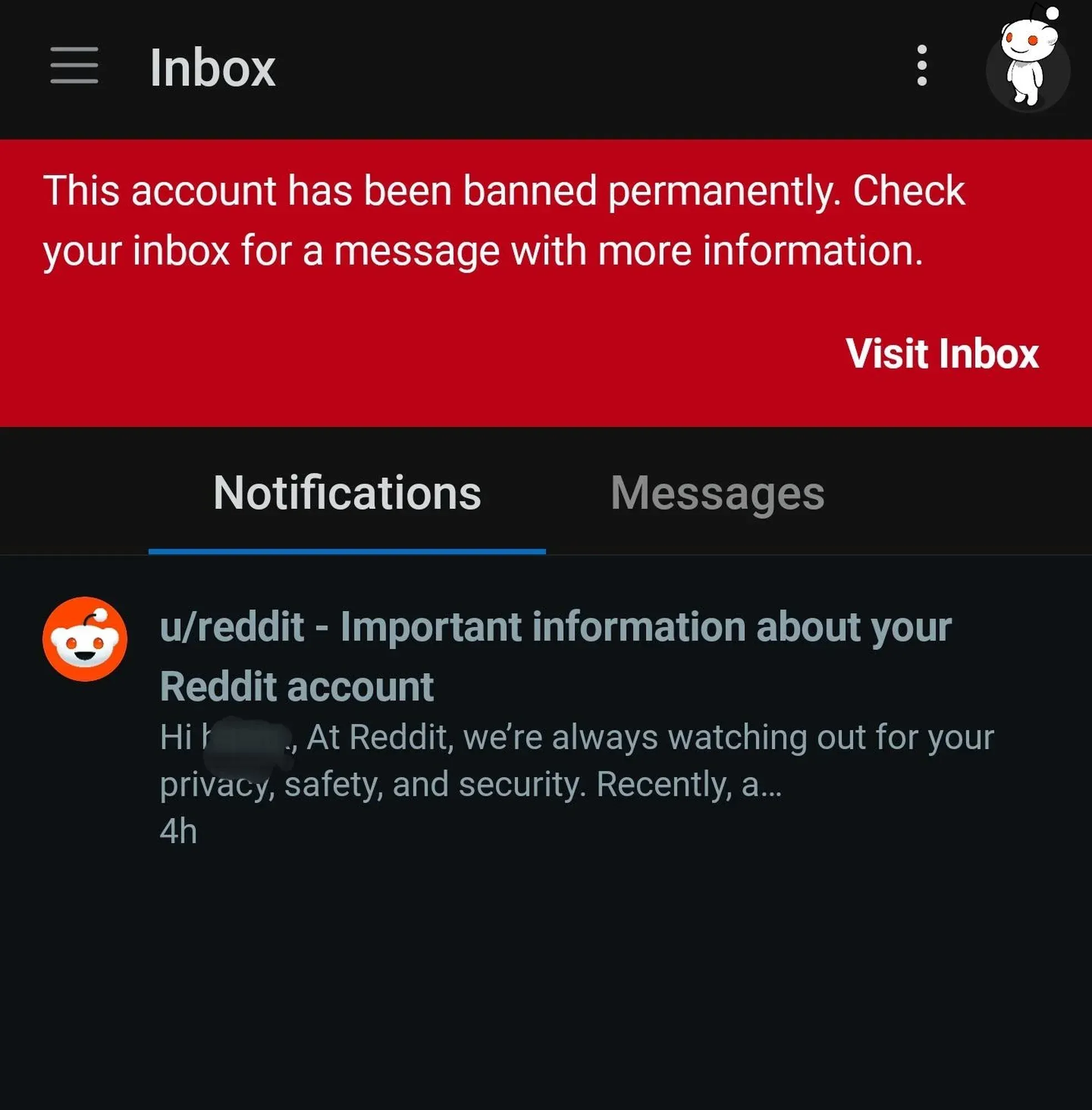
Risks of Using Incognito Mode for Multi-Accounting
Using incognito for multi-accounting in modern conditions is a high risk of detection. Outwardly it seems that profiles are separated, but at the system level, they remain linked.
Let's look at how this happens in practice.
Imagine a situation: you open several incognito tabs and try to register several profiles via VPN on a platform with anti-fraud. The email and IP will differ, but the device parameters remain the same.
Here's what happens next:
Profile linking by fingerprint. The system collects technical device parameters during each registration. Despite different emails and IPs, the fingerprint matches: graphics, fonts, screen, system characteristics. This is enough to link profiles together.
Shared restrictions. Linked profiles will be analyzed together. If one of them raises suspicion, restrictions apply to the rest as well.
Trust decline. A ban doesn't always follow immediately. More often, trust is reduced first: working conditions worsen, restrictions appear, and instability occurs.
Frozen funds. During blocks, funds in the balance may hang without the possibility of withdrawal across the entire account network.
Problems with new registrations. The device falls into the list of suspicious ones. New registrations from it go worse or immediately receive restrictions.
Dividing Tasks: When Incognito Is Enough and When Antidetect Is Needed
These tools solve different tasks. Incognito mode is needed for local privacy inside the browser. Antidetect is used for profile isolation and working with multiple accounts without intersections.
When incognito mode is enough:
- Checking output without personalization. Viewing search results or recommendations without the influence of browser history.
- Logging in from someone else's device. Quickly accessing email, messenger, or service without leaving saved data.
- Bypassing simple restrictions. Reading materials on sites with a limit on the number of views.
- Website testing. Checking how a site opens for a new user without saved data.
These scenarios don't require dividing profiles at the system level. Local data cleaning and launching a new session are enough. When it comes to working with multiple profiles, requirements change. In such tasks, incognito is no longer sufficient.
When you can't do without antidetect:
- Working with multiple profiles. Any tasks where it's important that profiles don't intersect with each other.
- Traffic arbitrage and advertising. Managing multiple cabinets and launching different bundles without intersections.
- E-commerce. Maintaining multiple stores or accounts on platforms with strict rules.
- SMM and farming. Mass work with social networks, warming up and maintaining several profiles.
Conclusion
Incognito mode is a tool for local privacy, not anonymity. It doesn't protect against anti-fraud systems, doesn't hide the device, and doesn't prevent accounts from being linked together. Attempting to use it for multi-accounting almost always leads to blocks and loss of money. An antidetect browser solves this problem differently: it creates a separate, logical, and plausible digital identity for each profile. This is exactly the approach that allows stable work with traffic and reduces risks.
Frequently asked questions
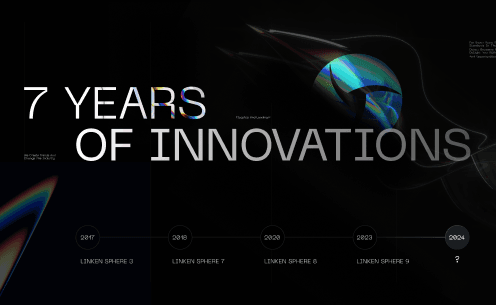
Linken Sphere 7th anniversary

Using LS with OBS Studio
This is a comprehensive guide that will help you implement video stream substitution in Linken Sphere without the risk of detection by anti-fraud systems.

Integration guide: Webshare + Linken Sphere
In today's digital landscape, maintaining privacy and anonymity online is more important than ever. Using an anti-detect browser like Linken Sphere is a powerful step towards safeguarding your digital identity. However, to maximize its effectiveness, pairing it with high-quality proxies is crucial. In this article, we'll explore what proxies are, the benefits of using them with an anti-detect browser, and why Webshare proxies stand out as an excellent choice. Additionally, we'll provide a guide to integrating Webshare proxies with Linken Sphere to ensure seamless browsing and enhanced security.