
Multi-accounting in crypto: how it works, where it's used, and why it's needed
Multi-accounting is the creation and management of multiple accounts by a single user. In cryptocurrency, this approach is used to bypass the "one reward per person" restrictions and thereby increase the chances of winning and the final profit.
Crypto projects distribute tokens, bonuses, or access to sales to attract an audience and demonstrate the growth of the user base. By having multiple accounts, one user can participate in activities many times. If $1000 is paid for completing a task, then a farm of 50 accounts can theoretically bring in $50,000.
Where multi-accounting is used in crypto
Working with multiple accounts is applied in almost all segments of the crypto market where there is a direct financial incentive. The underlying logic is simple: the more activities and "per user" restrictions there are, the higher the benefit from scaling through accounts or wallets.
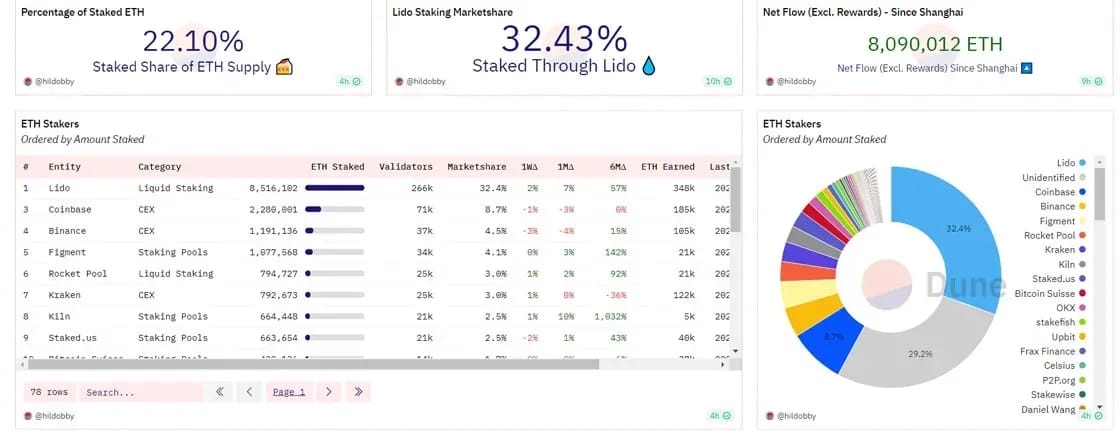
The first key area is decentralized finance and new blockchains. Young networks need testing, transaction activity, and liquidity. To attract users, they distribute tokens and bonuses for any actions that ensure the operation of protocols: staking, swaps, lending.
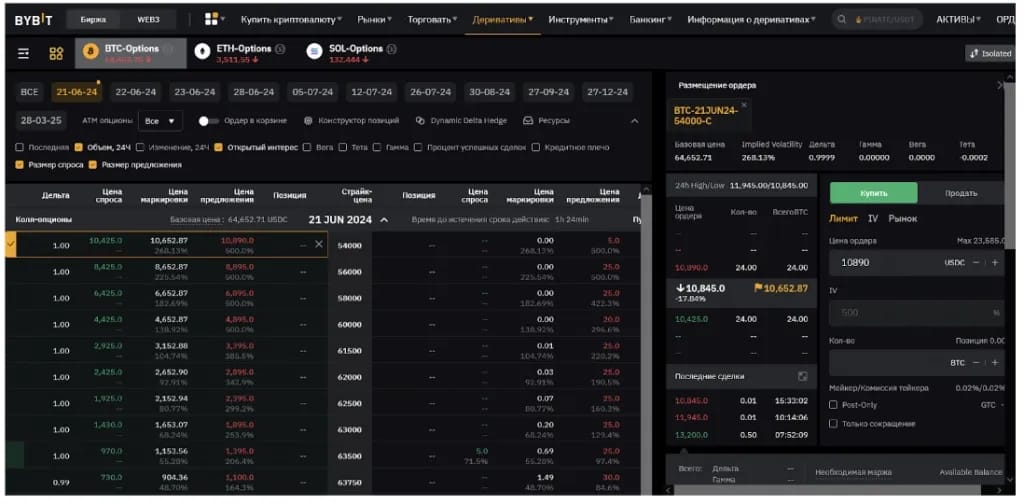
The second major segment is centralized exchanges, such as Binance, Bybit, and OKX. They regularly hold promotional campaigns with bonuses for registration, deposits, trading, and participation in activities. Thanks to large marketing budgets, even simple mechanics can generate stable income when scaled.
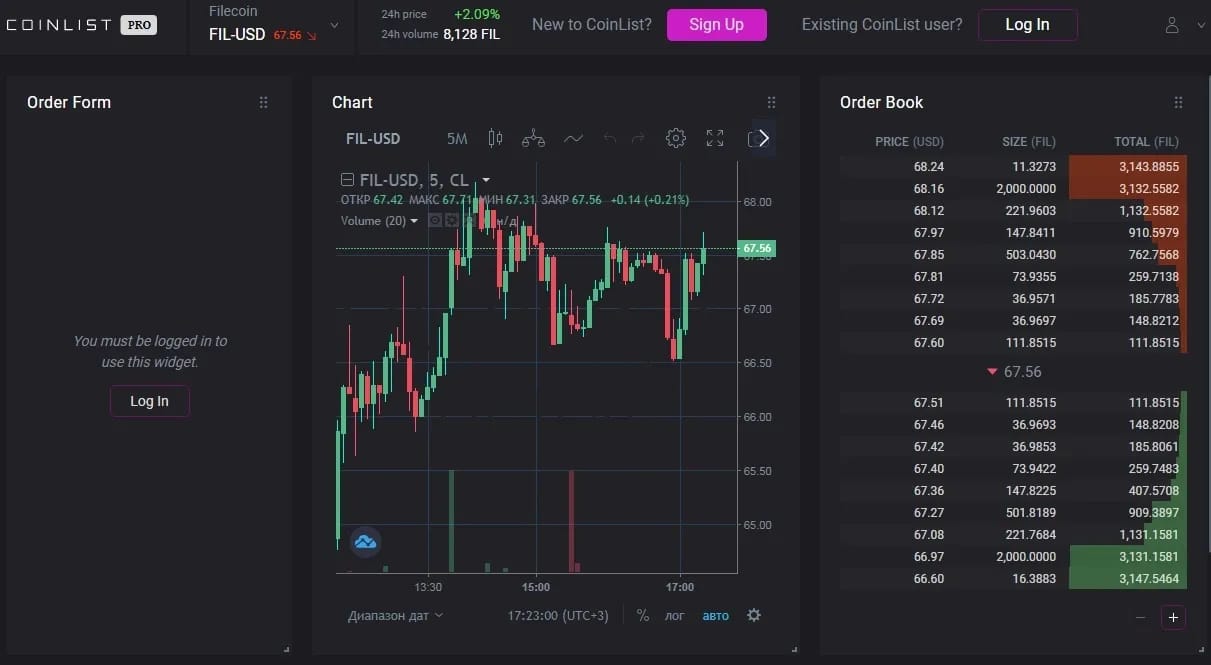
The third area is platforms for token sales and launchpads. Here, the right to the initial purchase of tokens before they enter the open market is distributed. Usually, there are strict limits per participant, so the main way to increase the result is to participate through multiple profiles and applications.
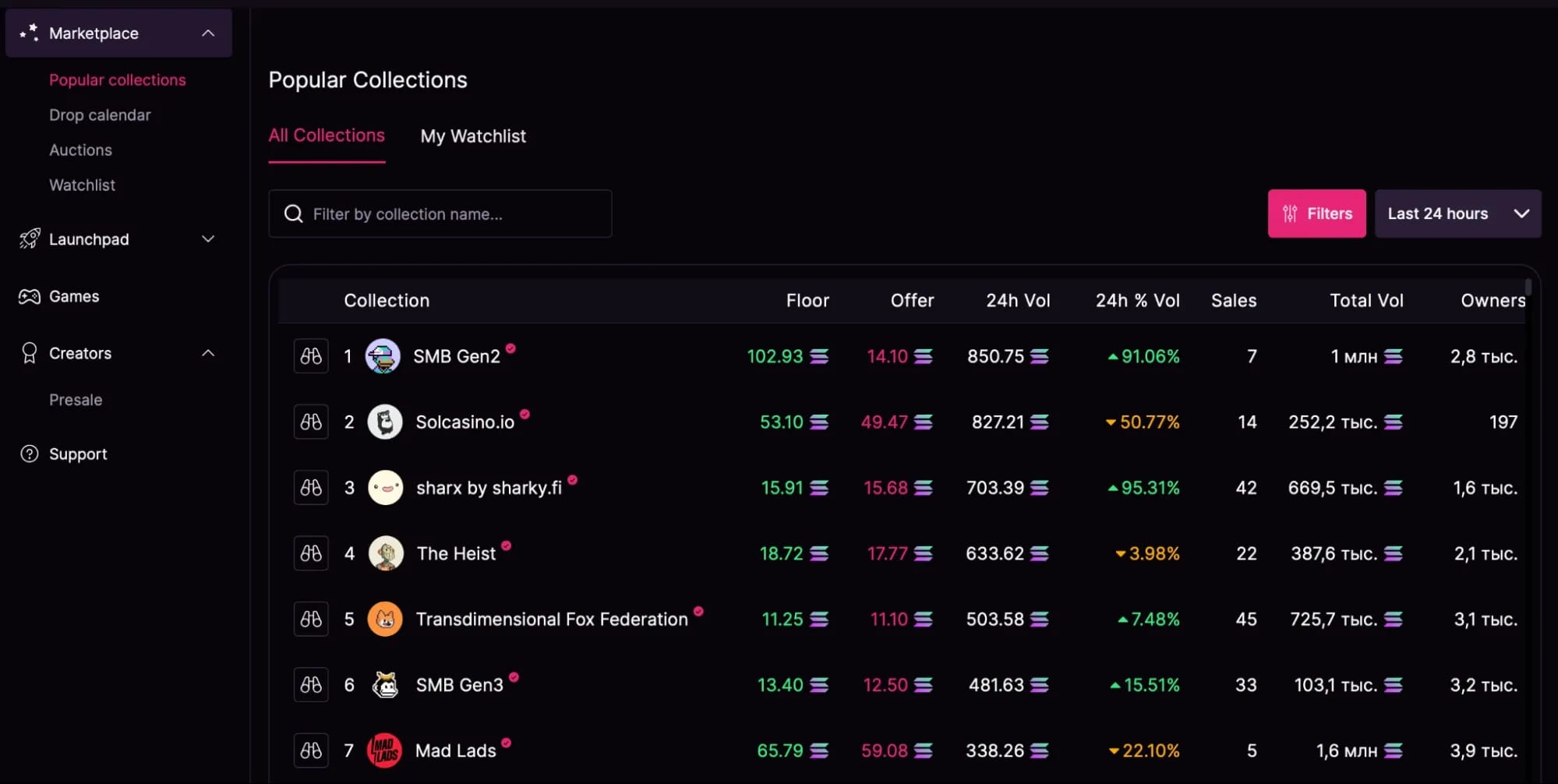
The fourth niche is the NFT market and related launchpads. Deficit is artificially created in this segment: projects limit the number of purchases per wallet and introduce access via whitelists. This makes scaling particularly effective, as each additional application increases the chance of gaining access to an early purchase.
The social Web3 segment stands out separately. This involves quest platforms and marketing hubs where projects pay for activity: subscriptions, reposts, participation in discussions, and completing tasks. Such services act as a connecting link between startups and the audience, and the task system is easily scaled through a large number of accounts.
Main schemes for earning on multi-accounting
Depending on what a crypto startup or exchange is willing to pay users for, farmers apply different strategies to extract profit. Let's look at the key ways of earning in more detail.
Scaling probability in lotteries
This scheme is used where rewards are distributed randomly. If the chance of winning the right to buy a token or NFT is one percent, a regular user's single account will most likely get nothing.
By driving a hundred profiles into the system, the farmer guarantees themselves one or two winning tickets. This mechanic is actively used on launchpads and in whitelist raffles.
Abuse of trading volumes
Wash-trading is used in projects that reward users for generating commissions or providing liquidity. If a platform promises to divide a token pool among active traders, the task of the multi-account is to artificially inflate statistics.
Capital is fragmented into multiple wallets, and special scripts begin transferring funds between them, creating the illusion of active trading. The money maker's task is to take leading positions in the ranking and claim the main part of the prize pool.
Collecting fixed bonuses
This method is built on scaling routine micro-tasks. Often, exchanges or crypto platforms pay small amounts for simple actions — for example, they credit $5 for passing a test about a new blockchain. Doing this manually a thousand times is irrational, as it would take weeks of monotonous labor.
Manual labor on such a scale is pointless, so the process is fully automated. For this, ready-made scripts are written independently or ordered from programmers — algorithms that accurately imitate real user mouse movements and keystrokes.
The software connects to a grid of profiles and clicks through the necessary answers on thousands of accounts in a few hours. As a result, penny bonuses add up to a solid profit.
Hunting airdrops and retro-drops
A retro-drop is the distribution of tokens to users who interacted with a project at an early stage. The idea is to reward those who tested the network, paid fees, and provided initial liquidity before the coin entered the market. Historically, top distributions brought thousands, and sometimes tens of thousands of dollars per wallet, which turned the hunt for drops into a separate industry.
The work begins with creating dozens, or more often hundreds, of isolated wallets. Next, the "warming up" process is launched — artificially building a transaction history. The task is to bring in initial capital through official bridges, inflate the exchange volume on local DEXs, and interact with the network's key smart contracts.
The main problem today is advanced project analytics that purposefully look for and ban multi-accounting. Therefore, primitive algorithms no longer work: modern scripts imitate the behavior of a live person. They make random pauses between transactions, change the sequence of protocols, and necessarily leave an irreducible balance so the wallet does not look like a squeezed-out, one-time dummy.
Abuse of bonuses and referral programs
Exchanges spend large budgets on user acquisition, so their bonus and referral programs can be scaled. The income is built on two main mechanics — referral chains and working with bonuses.
In the first case, a chain of accounts registered under each other via referral links is built. Trading activity is created at the lower levels, generating commissions. A portion of these commissions returns to the top accounts as cashback.
In the second case, deposit bonuses are used. Two accounts are created, and a bonus is credited to each. Then opposite leveraged positions are opened: long on one account, short on the other. As a result, one account goes into a loss, and the second locks in a profit. Due to the bonus funds, the overall result remains positive, and this profit can be withdrawn.
Working with centralized exchanges
The main barrier when working with major exchanges is the mandatory identity verification by documents. For scaling, ready-made accounts registered to third parties and purchased from middlemen are used.
Such a model quickly pays off through participation in launchpads, where tight limits per user apply. Capital is distributed across a grid of accounts, allowing bypass of restrictions and collection of a larger allocation.
A similar principle applies to coin listing votes. The reward depends on the number of votes cast, so the scale directly affects the final result: more accounts mean more rewards.
NFT and launchpads
Creators of digital collections always limit minting to one or two pictures per wallet to protect against monopolists. This can be bypassed using custom smart contracts that allow buying out dozens of NFTs from different generated addresses in a single transaction.
To obtain the right to an early purchase of promising assets, projects often require social activity: chatting, retweets, and likes. This process is also scalable. Pre-prepared social media accounts are used, software is connected, and actions are performed en masse — profiles automatically enter giveaways, like, and retweet. Through sheer volume, such applications take up a significant portion of the spots, pushing out regular users.
Tools for multi-accounting
Logging into a hundred profiles through regular incognito mode in Chrome is a guaranteed path to getting banned. Modern anti-fraud systems have long stopped looking only at cookies. They collect a device's digital fingerprint, which includes data on the graphics card, screen resolution, installed fonts, plugins, and even the operating system language. For safe multi-accounting, you will need an entire arsenal of specialized software:
- Anti-detect browsers (Linken Sphere, AdsPower, Dolphin Anty). This software works at the browser core level, isolating profiles and spoofing hardware and software parameters. For any security system, each such profile looks like a unique computer of a real person.
- Proxy servers. A unique digital fingerprint is not enough if a single IP address is used for all farm traffic. Each profile in an anti-detect browser must be linked to its own proxy. You cannot use cheap server options from data centers: security algorithms instantly see the connection from a hosting provider. Safe operation is ensured by residential or mobile proxies belonging to real home computers or cellular subscribers.
- Consumables for social networks. Full-fledged operation of crypto profiles requires X or Discord. Creating them from scratch is long and risky, so it makes sense to mass-purchase ready-made warmed-up accounts. The main safety rule is to avoid classic login and password authorization; instead, session tokens and cookie imports are used. This method allows logging into an account under the guise of a simple page refresh, eliminating unnecessary attention from algorithms.
- Automation software. Managing large grids of profiles quickly hits human physical limits. All routine work is taken over by custom Python scripts and scenarios in environments like Browser Automation Studio. The program connects directly to the anti-detect browser and manages profiles on its own, clicks on interfaces, and confirms transactions. Automation allows the farm to work around the clock and eliminates human error.
- Exchange sub-accounts (e.g., OKX). The blockchain is absolutely transparent. On-chain analytics will instantly link wallets into a connected cluster if starting capital is directly distributed from a single personal address. A centralized exchange acts as a legal mixer. It is necessary to create dozens of isolated sub-accounts within your main account, generating independent addresses. This method allows you to safely distribute money and collect profits, completely breaking the transactional link.
Conclusion
Multi-accounting has turned crypto activities into a systematic business of draining marketing budgets. Moneymakers bypass project reward delivery limits en masse, multiplying their final profit. The security of such farms relies on anti-detect browsers, high-quality proxies, and automation scripts that closely mimic the actions of living people.
Frequently asked questions
- It depends on the niche. For testnets and social quests, a couple of tens of dollars will be enough to pay for proxies, software, and penny fees. For retro-drops in major blockchains, you will need from $50 to $100 per wallet for warming up and maintaining an irreducible balance. On exchanges and token sales, the bill goes into thousands of dollars, as capital must be smeared across dozens of accounts to get a worthwhile allocation.
- This is one of the main non-technical risks. A drop (the person under whose name the account is registered) can write to exchange support at any moment, claim an account hack, restore access via passport, and take all your money. Therefore, you must work only with trusted sellers who provide a guarantee, and not hold primary capital in such accounts.
- In decentralized networks, wallets are simply blacklisted. They lose the right to the reward, but the money itself on the balance remains under the user's full control — only time and funds burned on fees are lost. On centralized exchanges, an account can be frozen and a video call may be demanded for unlocking, which leads to a loss of funds if the proxy owner is unavailable.
- Creating hundreds of anonymous wallets may be a violation of a specific startup's rules, not the law. There is no criminal liability for this. But buying other people's passports and selfies to pass KYC on centralized exchanges is already a gray or black legal area, which in many countries is classified as identity fraud.
- The entry barrier has become radically higher, but the industry is alive. While a couple of years ago projects handed out money for two transactions from a single IP address, now they use cluster analysis to find links. Weak money makers with cheap software are indeed filtered out and go into the red. For professionals, this is a plus: random people leave the market, competition for reward pools drops, and profit grows.

Why Google Blocks Accounts and What Your Antidetect Has to Do With It
Google has once again complicated the mechanisms of digital identification by deploying a new, more sophisticated layer of protection based on proprietary HTTP headers. This quiet change caught most of the market off guard, triggering a wave of rushed updates. While others hastily released superficial 'fixes', we realized that we were dealing not with a minor issue but with a fundamental shift that required deep and comprehensive analysis.
SOCKS vs HTTP Proxy: What’s the Real Difference and Which One to Choose?
There are times when you don’t want a website to link the request back to your device. That’s where a proxy comes in, it acts like a middle layer and sends the request for you. The site sees the proxy’s info instead of yours. It’s a go-to trick when you’re trying to see a page that’s not available in your region, pull content that’s restricted by location, or avoid hitting a wall when sending lots of requests.

The Best Alternative to OBS Studio
Working with a webcam on many online platforms can turn into a real challenge. A strict oval or rectangular frame appears on the screen, but your image doesn’t align perfectly with it. As a result, the system blocks further progress, demanding perfect alignment, and your workflow is disrupted before it even begins.